When Authority Becomes the Weapon
In early 2025, fraudsters weaponized something we've trusted for millennia: the human voice. They cloned Defense Minister Guido Crosetto's voice with surgical precision, then called Italy's business elite with an urgent plea. Journalists were supposedly kidnapped. Lives hung in the balance. Money needed to move fast.
At least one executive believed it completely. Nearly one million euros transferred before police intervention froze the funds. The victim's trust wasn't misplaced. Their recognition of the minister's voice was accurate. The technology had simply made accuracy meaningless.
The 20-Second Vulnerability Window
Modern voice cloning needs just 20-30 seconds of source audio. For public figures like Defense Minister Crosetto, that material exists everywhere: press conferences, interviews, parliamentary sessions. The fraudsters didn't need to hack anything or steal private recordings. They simply harvested public appearances and fed them to AI.
The result? A synthetic voice indistinguishable from the original. Even sophisticated business leaders, people trained to spot deception in high-stakes negotiations, fell for it completely. When your ears can't tell the difference, what defense do you have?
Beyond Individual Victims: Institutional Damage
This attack targeted more than bank accounts. It weaponized institutional trust. When fraudsters impersonate a Defense Minister, they don't just steal money. They undermine confidence in government communications. Every future call from that office now carries doubt.
Consider the cascading effects:
- Business leaders become hesitant to respond to genuine government requests
- Official communications require additional verification steps
- Public trust in institutional voices erodes
- The cost of conducting business with government increases
The Milan executive lost money. Italian institutions lost something harder to replace: credibility.
The Authentication Crisis Spreads
This isn't isolated to Italy or government figures. Voice cloning attacks increased 700% in 2024 according to security firm Pindrop. The pattern repeats globally:
Corporate Impersonation: CEOs' voices cloned to authorize fraudulent wire transfers Family Emergency Scams: Children's voices synthesized to panic parents into sending money Romance Fraud: Dating profiles backed by cloned voices of attractive public figures
Each attack follows the same playbook: harvest public audio, clone the voice, exploit trust relationships, profit from confusion.
When Your Voice Becomes Evidence
Here's the deeper problem: if voices can be faked, how do you prove yours wasn't? Imagine facing accusations based on a phone recording that sounds exactly like you. Your denial means nothing when the evidence is perfect.
This reverses the burden of proof. Instead of accusers proving guilt, you must prove innocence. But how do you prove a negative when the technology creates flawless fabrications?
Traditional alibis fall short:
- "I was at home" can't counter a phone recording
- Witness testimony becomes he-said-she-said
- Phone records show calls happened, not who made them
The Defense Minister case shows this vulnerability in real-time. If Crosetto faced accusations about those calls, what would prove his innocence?
Building Multi-Layered AI Defense
The solution isn't better detection. It's prevention through proof. The AI Defense Suite provides comprehensive protection against voice cloning and executive impersonation attacks through three specialized tools.
Agent Safe would have protected the Milan executive at the moment of attack. This 9-tool security suite analyzes all incoming communications across phone calls, emails, SMS, WhatsApp, and other platforms for signs of social engineering and impersonation. When that cloned voice call came through, Agent Safe would have flagged the urgent financial request, the pressure tactics, and the unusual communication pattern.
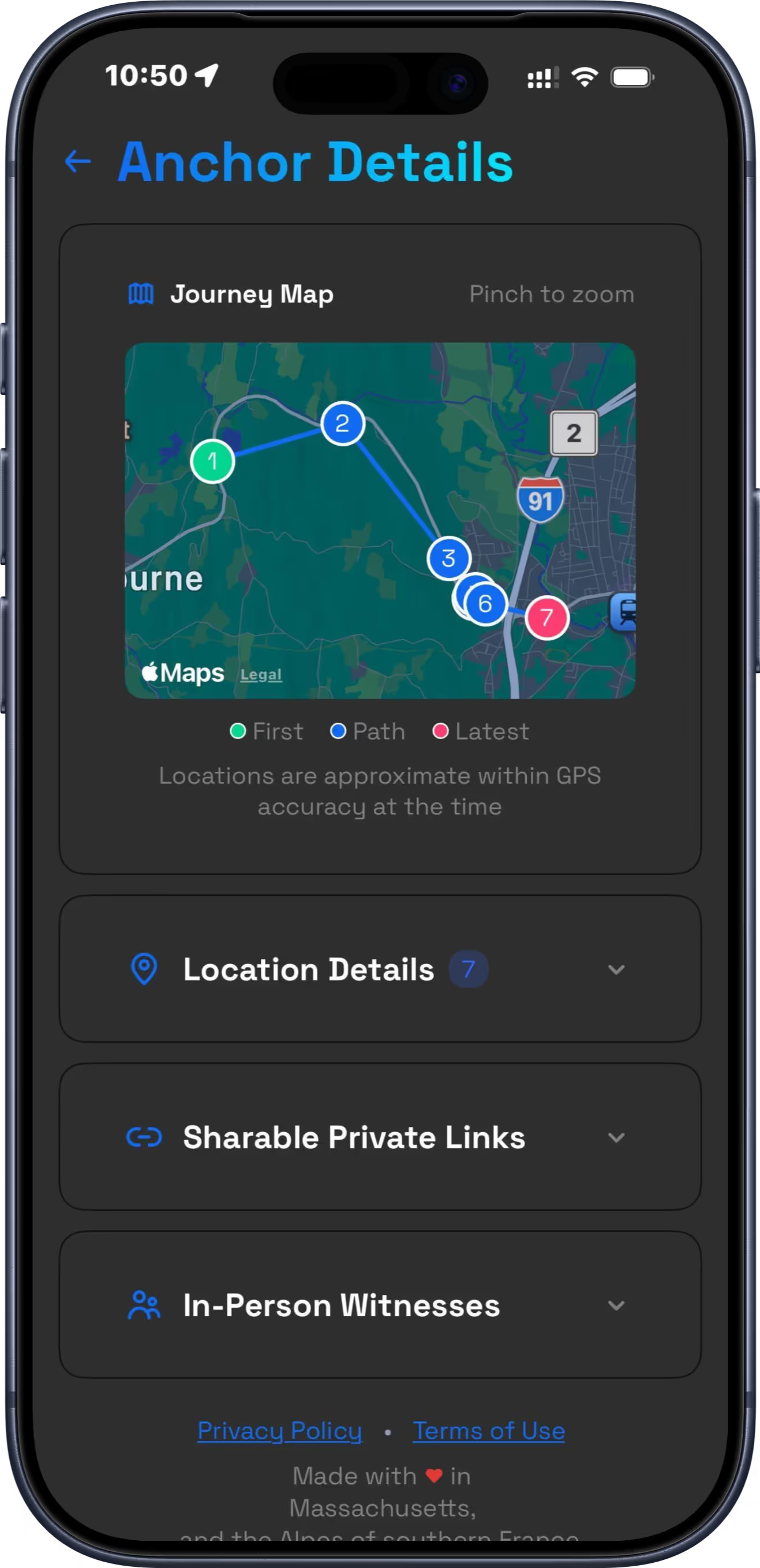
Meanwhile, Location Ledger creates unalterable proof of where public figures actually were. Every 15 minutes, encrypted location data gets recorded and anchored to World Chain's blockchain daily, creating timestamps that cannot be manipulated by anyone.
The Three-Layer Defense
Layer One: Real-Time Protection Agent Safe monitors all communication channels for impersonation attempts, phishing, and social engineering tactics. It would have immediately flagged the Defense Minister impersonation call as suspicious.
Layer Two: Location Verification Location Ledger automatically captures encrypted location data every 15 minutes. When Minister Crosetto was accused of making those calls, he could have provided cryptographic proof of his actual whereabouts.
Layer Three: Human Authenticity Proof of Life creates biometric-verified selfies that prove a real human (not AI) was present at specific times and locations. These "Proofies" use Face ID or Touch ID with blockchain timestamps.
From Defense to Offense
This protection extends beyond personal defense. Business executives can verify their communications are legitimate. Public figures can demonstrate their actual activities when faced with synthetic audio evidence. Organizations can protect against CEO fraud and business email compromise.
The Milan case would have unfolded differently with AI Defense Suite protection. Agent Safe would have warned the executive about the suspicious call. Location Ledger could have immediately provided proof of Minister Crosetto's whereabouts. The fraud would have collapsed within minutes instead of succeeding for hours.
The Window Is Closing
Voice synthesis improves daily. Detection methods lag behind creation tools. The gap between synthetic and real continues shrinking. Soon, even experts won't distinguish between authentic and artificial audio.
This makes proactive protection essential. You cannot wait until facing accusations to build your defense. The evidence must exist before you need it, captured automatically and stored immutably.
Every phone call you didn't make, every location you weren't at, every conversation you didn't have becomes provable. Not through better lie detection, but through unalterable truth creation.